Security is not a cost.
It's a savings line.
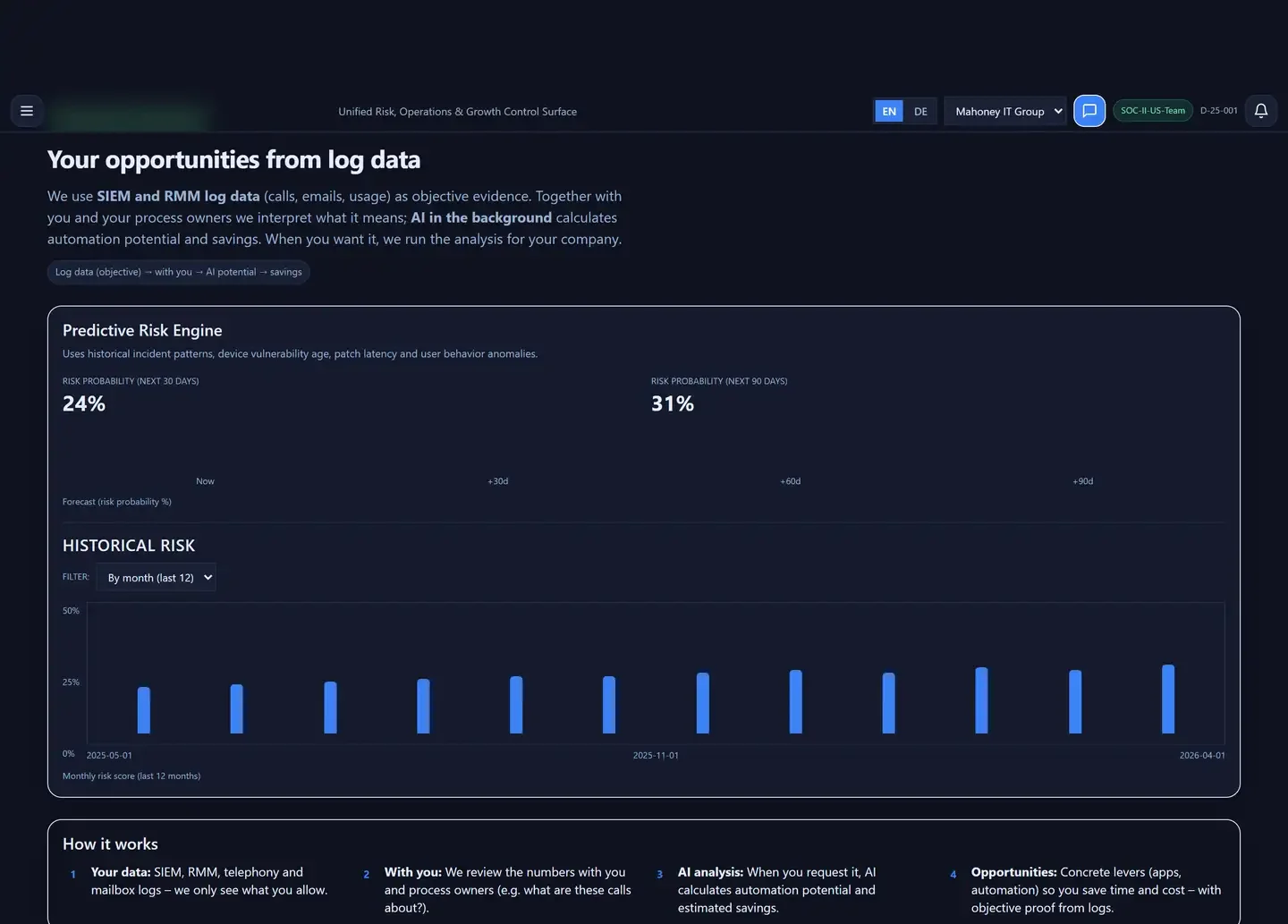
Mahoney Grow surfaces how many hours of repetitive work and how many dollars of avoidable cost sit in your SOC and RMM telemetry — no new sensors, no new contracts.
Security as a Growth Engine. Not a Cost Center.
Mahoney Grow translates your own SOC and RMM telemetry into cybersecurity ROI — so security stops showing up only as a line in the expense column.
*Modeled outcomes from real engagements (anonymized). Your numbers will differ. Risk and growth models are advisory and do not constitute financial or legal advice.

From Console to Boardroom
From Hidden Workflows to Finance-Grade KPIs.
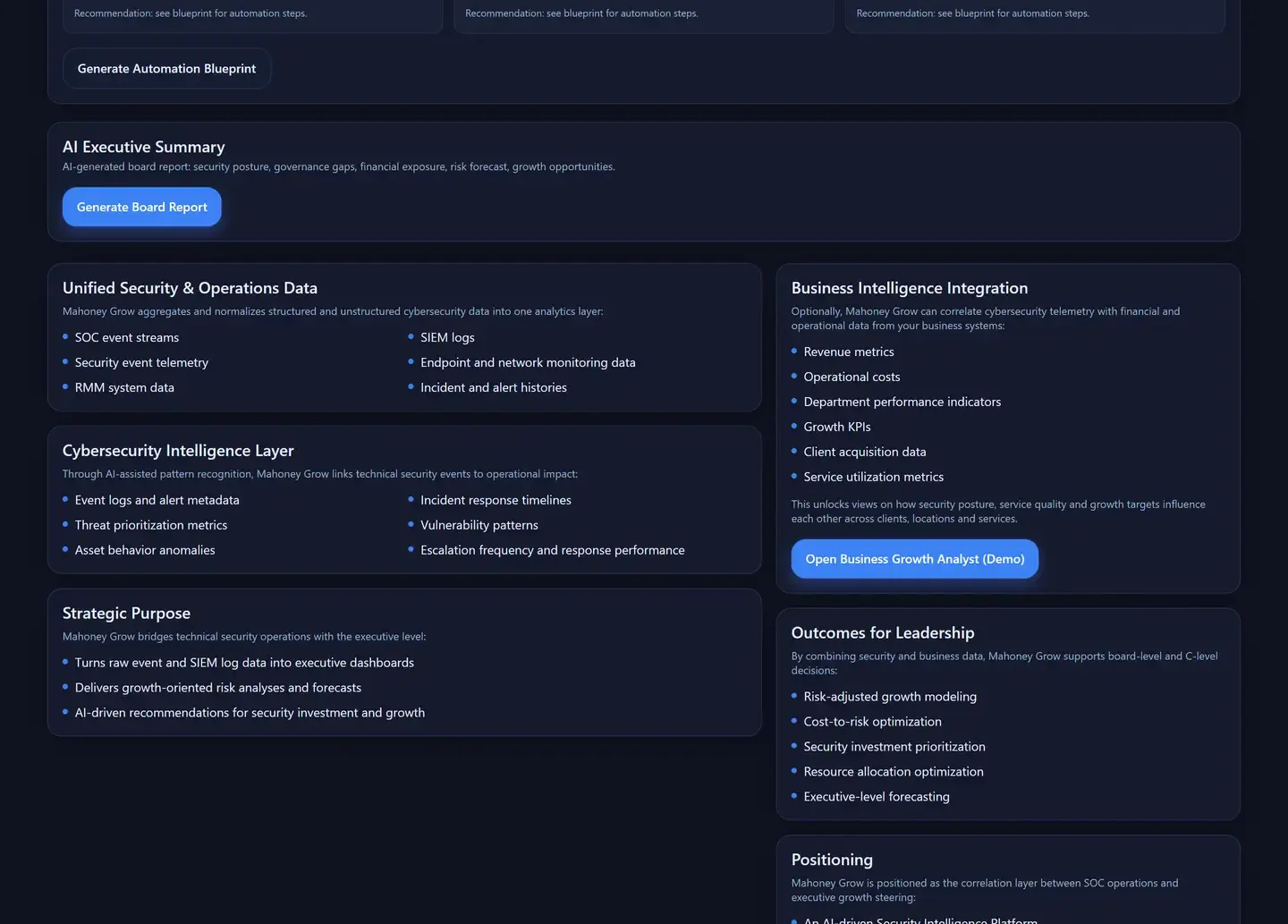
Operations runs your SOC. Governance maps your controls. Growth Intelligence turns both into answers your CFO can act on — in the same Mahoney Control instance, on the same telemetry, with the same opt-in principle.
Talk to a Mahoney IT SpecialistSecurity as a Cost Center vs. Security as a Profit Lever
Security as a Cost Center
Budget Questions Without Answers
Every quarter the finance team asks what the security spend produced. The SOC has dashboards full of alerts — none of it translates into a line a CFO can approve.
Board Presentations in PowerPoint
Posture statements, severity counts, tool screenshots. Nothing that tells the board whether risk actually moved since last quarter.
Hidden Workflow Cost
Repetitive manual work buried in tickets and logs. Nobody measures it, so nobody reclaims it — year after year.
Frameworks as Audit Tax
ISO 27001, NIS 2, SOC 2 show up only as cost items for the audit folder, never as inputs to a growth conversation.
Security as a Profit Lever
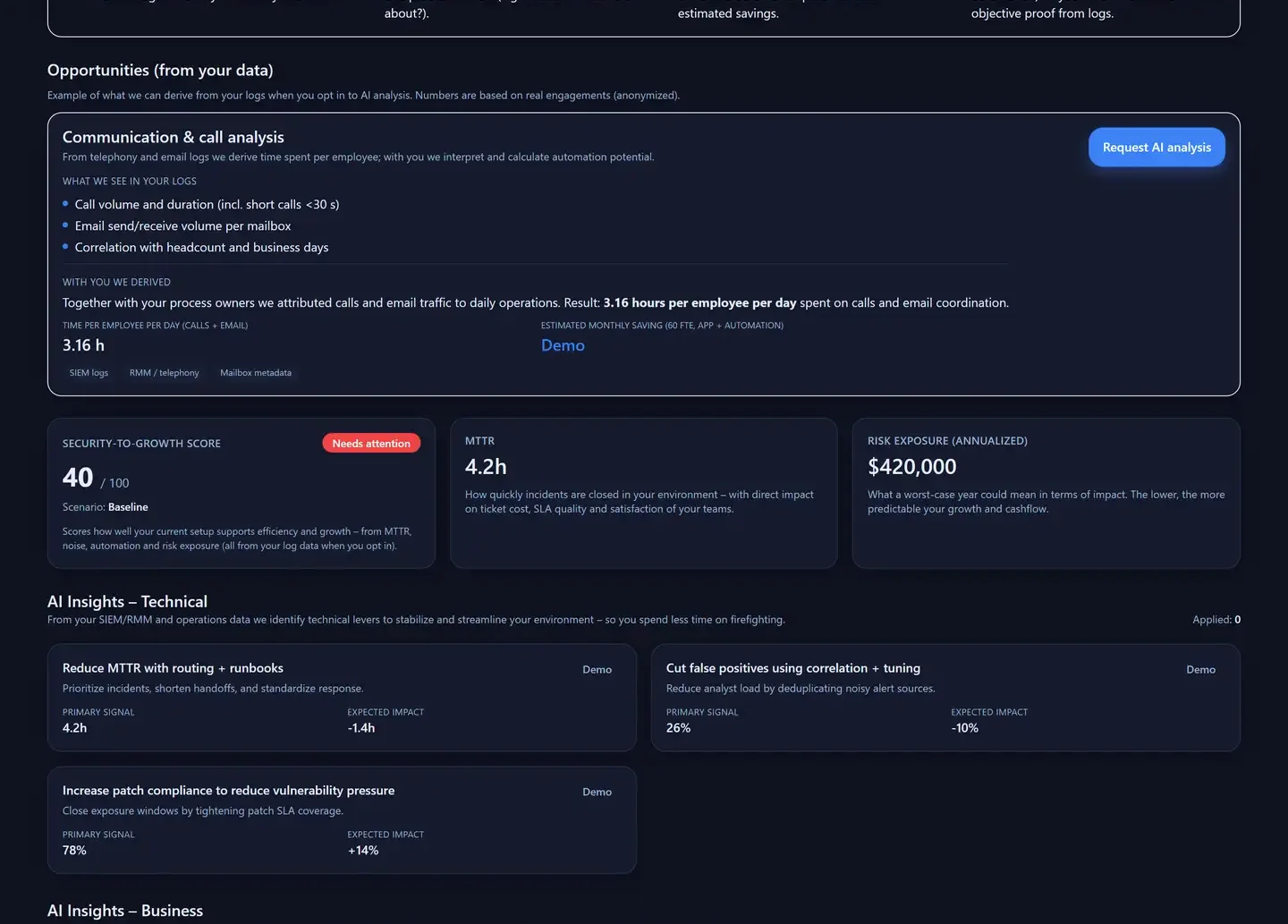
Dollar-Denominated Answers
Risk exposure, revenue retention and gross-margin impact — modeled from the telemetry your SOC already collects, in the same language the CFO uses for every other security investment.
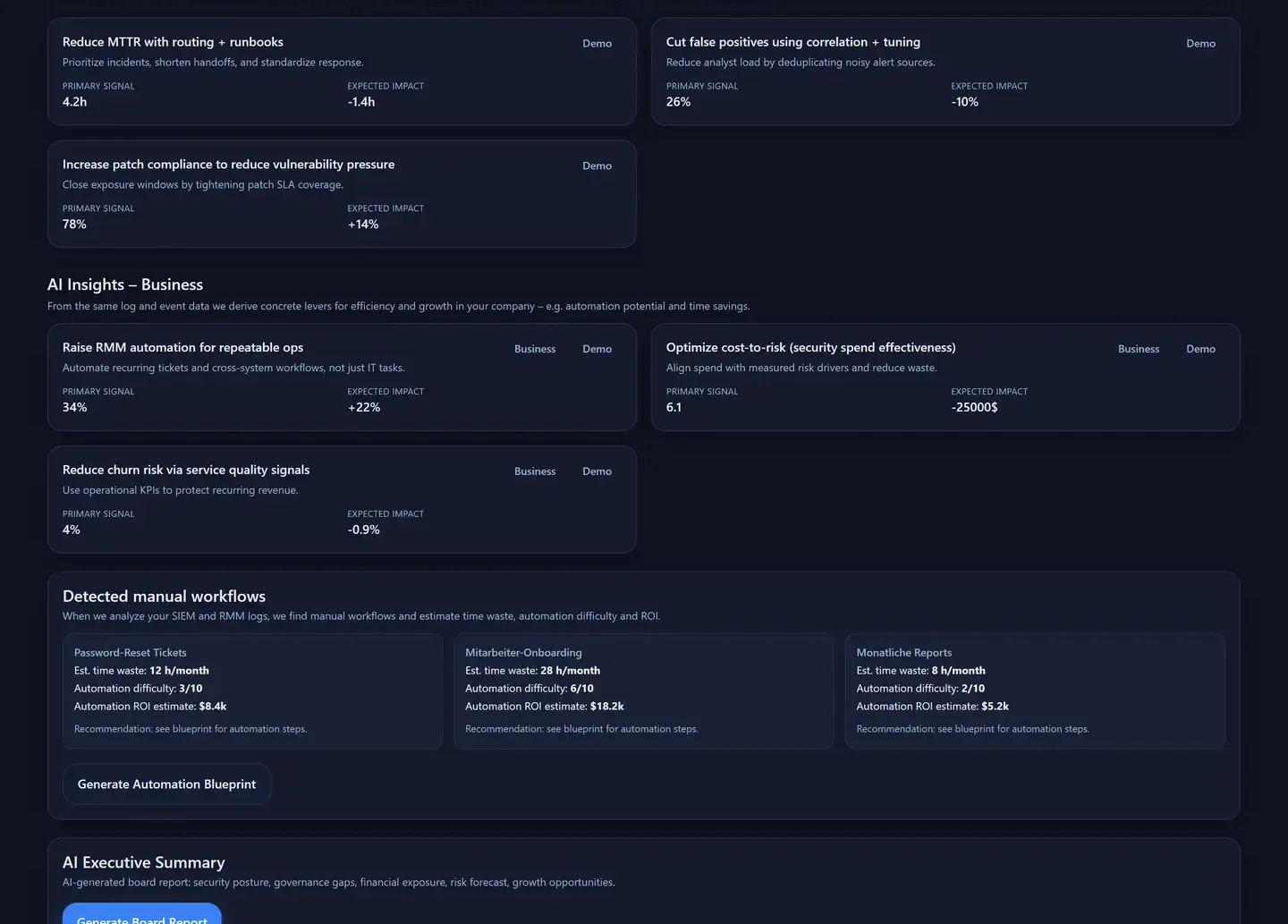
Board-Ready KPIs
Three leadership KPIs (Security-to-Growth Score, MTTR, Risk Exposure) plus a generated executive summary — ready for the next leadership meeting without a PowerPoint rebuild.
Automation Discovered in Your Logs
Repetitive workflows identified automatically and quantified in hours and dollars — $31.8K/year in reclaimed analyst work across three representative workflows*.
Frameworks as Leverage
Controls mapped to ISO 27001, SOC 2 Type II, NIS 2, DORA and NIST CSF — the same evidence feeds the growth conversation, not just the auditor's folder.
*Modeled outcomes from real engagements (anonymized). Your numbers will differ. Risk and growth models are advisory and do not constitute financial or legal advice.
Growth Intelligence — Frequently Asked Questions
Does Mahoney Grow process our data automatically?
What data sources do we need to start?
Are the modeled numbers guaranteed?
How does Growth Intelligence connect to Operations and Governance?
Is Mahoney Grow a separate product we have to license?
How do you calculate cybersecurity ROI?
Your data stays yours · Security operations since 2018 · Data residency EU / US / Asia — your choice · Your tools stay yours
ISO 9001:2015 certified by DEKRA · 24/7 SOC operations · Three pillars, one platform
See Mahoney Grow in Action
30 minutes. No sales pitch — just an honest walk-through of how Mahoney Grow turns your SOC and RMM telemetry into a CFO-ready answer.
Mahoney Control maps controls to: ISO 27001 · SOC 2 Type II · NIS 2 · DORA · NIST CSF
Mahoney Grow analyzes your data only when you explicitly request it. No background processing, no shadow data flows. Risk and growth models are advisory and do not constitute financial or legal advice. Certification itself is awarded by independent auditors — Mahoney Control prepares your organization for that audit.